Cyber Security Risk Assessment for SMEs in Qatar: 10 Controls to Prioritise Now
Cyber security conversations often become too technical too quickly. Business owners hear about ransomware, zero-day threats and compliance pressure, but what they really need is a clear way to decide what should be fixed first. That is the value of a risk assessment. It converts security from a vague fear into a practical action list.
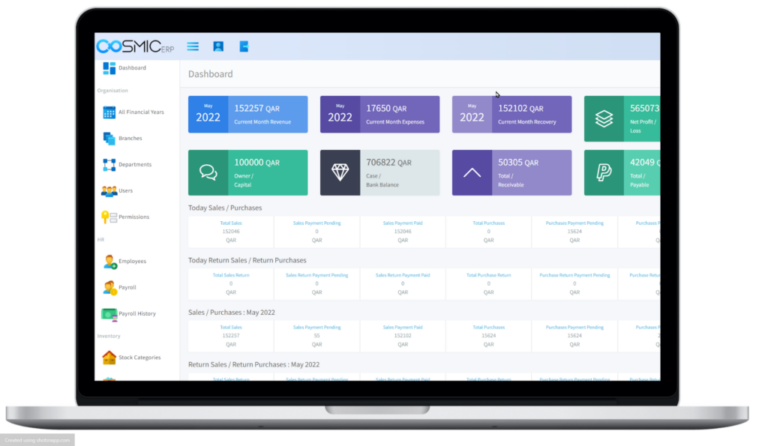
For SMEs in Qatar, this matters even more. Many organisations now run cloud applications, online payment flows, remote access tools, outsourced IT support and integrated websites. Every one of these creates a point of exposure if access is weak, backups are untested or staff behaviour is unmanaged.
1. Identify where the business would actually feel damage
Start with the assets that would hurt most if they became unavailable or exposed. That usually includes finance data, customer information, quotation history, contract files, payroll records, stock data and operational systems. A risk assessment should rank these assets by business impact, not by technical interest.
When this step is missed, companies end up spending money on low-value tools while leaving core operational exposure untreated.
2. Lock down identity and access management
Weak passwords and shared logins remain one of the easiest paths into a business environment. Multi-factor authentication should be enforced for email, cloud systems, admin panels and remote access. User accounts should map to real job roles, and old employee access should be removed immediately.
This is particularly important when multiple services are connected through a cloud computing environment or external platforms such as CRM, finance and collaboration tools.
3. Test backup quality, not just backup existence
Many teams say they have backups, but they have never tested recovery speed, file completeness or restoration ownership. A real control means you know where critical backups live, how quickly they can be restored and who is responsible when an incident happens.
For ransomware resilience, offline or isolated backup copies matter. If an attacker can encrypt production data and the backup environment at the same time, the recovery plan is weaker than it looks.
4. Review endpoint and patch discipline
Laptops, desktops, servers, mobile devices and network appliances all need a defined patch process. Unsupported operating systems, outdated plugins and neglected firewall firmware continue to create avoidable risk. A risk assessment should list which systems are behind and how often updates are applied.
5. Reduce email and phishing exposure
Email remains one of the main entry points for compromise. Staff need practical phishing awareness, but training alone is not enough. Businesses should also review mail filtering, domain protection, suspicious login alerts and approval controls for payment requests or vendor account changes.
6. Check supplier and third-party dependencies
Most SMEs rely on external software vendors, hosting providers, managed service partners and payment gateways. A weak supplier can still become your problem if they hold your data or connect into your environment. This is why cyber risk should be reviewed alongside vendor management, contract terms and support access.
Where multiple business systems depend on each other, a structured integration review helps expose hidden security and continuity gaps across the stack.
7. Separate administrative privilege from routine work
Users should not browse the web, open attachments and run day-to-day work from high-privilege accounts. Separate admin identities reduce the blast radius when credentials are stolen. It is a simple control with significant value.
8. Improve visibility with logging and alerts
You cannot respond well to what you cannot see. Even smaller businesses benefit from centralised logs, suspicious sign-in alerts and a basic incident escalation path. This does not have to mean a large security operations centre. It means knowing where to look when something goes wrong.
9. Align cyber controls with operations and compliance
Security should support business continuity, audit readiness and client trust. If your company handles personal records, financial documents or regulated workflows, cyber controls should be mapped to those obligations. This is often easier when security planning is tied into broader IT consulting and governance rather than treated as a disconnected IT purchase.
10. Create a realistic incident response path
Every organisation should know who makes decisions if email is compromised, if a laptop is lost or if data becomes unavailable. Documented contacts, escalation rules, recovery priorities and communication ownership reduce confusion when minutes matter.
Conclusion
A cyber security risk assessment is valuable because it replaces guesswork with priorities. For SMEs in Qatar, the goal is not to copy enterprise bureaucracy. It is to protect the systems, data and workflows that keep the business trading.
If you need a practical security review linked to your cloud, applications and operating model, contact TFSBS. We help businesses turn cyber risk into a clear improvement roadmap.